Agenda Items
Decisions
Action Plans
Meeting Introduction Security Matters
The security of your data on the internet is of concern at various levels. We live in an interconnected world and the economies that we operate within depend upon the security of information and the technology that supports your security is a part of a bigger picture. The internet supports trillions of transactions and the global economy is dependent upon the security of the information on it. Can you imagine a row of clerks in a bank with sleeves rolled up manually writing up corporate cashbooks? The reality is that we have moved forward, jobs and the business process has changed. With the change has come creative new ways to build businesses and the technology that underpins the success is at risk, as has been the foundations of every econony that went before, because there are those with criminal intent who seek to hack, defraud, destroy or disrupt nations, companies and individuals. Unfortunately cybercrime has become a "team sport" and is not only conducted with fraudulent intent.
The bottom line is that if content is highly secret, then you need to keep it in a bunker and not on the internet. For other sensitive information, you need to assess the relative sensitivity of the content and the impact of the risk. There is much that can be done at various levels. For many, the likelyhood of data loss, is higher at preventable levels of data security.
Sound security practices can go a long way to protect customer data and strategic business process competitiveness. Close your eyes and imagine the lie of your golf ball on fairway with a monkey scratching himself right next to it. Will he take the ball and what could you have done to prevent this risk? The likelyhood of loss is high however, the impact of the loss is low provided that you do not let it get to you!
What can be done?
Content Security on Portable Devices
Board and meeting packs have always been a weak link in that the chain of custody is often broken. Have your meeting papers remained in your possession in a secure location? You know that many lever arch files of sensitive information find their way to bins and public disposal sites. In short, the whole exercise of building the paper mountain and then shredding it, all too often, becomes a nightmare. Shortcuts are taken, and sensitive information is at risk.
Compare this scenario with password protected documentation on an iPad where data transfer is encrypted at the highest level. Are you likely to leave your iPad unattended in an insecure area? Will you write your password on the back of the iPad?
Ask yourself; is my iPad, phone or laptop more secure than a lever arch file? Your day-to-day diligence in maintaining custody of your phone/ tablet is likely to be higher than that for a pile of Lever Arch Files.
Content security will be greatly enhanced by ensuring that staff understand the impact that the loss of data would have and you can audit the access controls to ensure that available mechanisms such as password or biometric acess controls are in place. In addition, laptops can be secured with cable locks to desks etc.
While laptops, phones and tablets enjoy a relatively high level of importance to their owners they do get lost or stolen. When this happens access controls become important. The level of understanding on this matter tends to be higher than for physical storage media such as hard drives and USB flash drives. The latter tend to get lost more often and they tend to be set up with less access controls. You can purchase flash drives with physical combination locks on them and you can secure data on portable devices with a variety of software dedicated to his purpose including:
Content Security on Table Top Devices.
Again, access controls can be considered as can cables/locks be used to secure PC's to desks. Afterhours building access and exit security can assessed.
Data Transfer
Accidents and Disasters
What if your laptop is destroyed in a car accident, it is lost in a flood, fire or you accidentally delete files? Whilst these eventualities are not malicious they have the same consequence. Again likelyhood and impact need to be considered in assessing your level of protection needed.
Do you need to maintain all data in a cloud with nothing on your device? Will weekly off site backups reduce the risk and impact of loss to acceptable levels?
Having secure backups is one solution is data loss. If backups are to be manually executed then staff need to be educated as the importance making backups and maintaining feedback checks can be considered to ensure that it is done.
Password Security
Strong passwords have the following characteristics:
• Have at least eight characters. • Do not contain your user name, real name, ID number, company name, or a complete dictionary word. • Contain upper and lower case letters, numbers, and symbols (!, @, #, $, %, etc.). • Are not used for multiple accounts or computers. • Keep passwords and PINs secret. Don’t disclose them to family, friends and colleagues. • Change your passwords at regular intervals, such as every 90 days. • Set your computer to hibernate or go into sleep mode, requiring a password to unlock it, when you step away for more than a few minutes. Document integrity
Sending files over the internet in original format such as word, excel, powerpoint ,pages, numbers, keynote etc., means that if they end up in the hands of others either directly or indirectly from the person that you sent them to they can easily be altered to misrepresent the contents that you supplied.
The MEETING PACK COMMUNICATOR can link to an Independent Webpage where a schedule of downloads are presented of documents that are downloaded by way of hyperlinks. The data transfers to recipients will be encrypted but once received documents in original format can easily be changed. Perhaps this is what is intended where one seeks work to be done on the document. Where the integrity of the document needs to be protected a level of comfort can be obtained from sending it as a PDF document.
This however does not mean that it cannot be altered, which if the recipient has Acrobat or Photoshop, as an example, can easily be done. The loading of the document to one of our content managers means that it will be opened online and the document will not have been transferred to the recipient. It can also be put behind a password. The latter two options adds to the level of security around the integrity of the document however it remains open to abuse. Schedules, for instance, can be copied from the screen for pasting into excel.
Registered Mail?
When you send e-mail it is equivalent to unregistered mail. "You lick the stamp and hope!" Registered mail means that you are notified of receipt. This is a mail setting that should be encouraged. An alternative is to have the recipient "collect" the files and to register the fact that it was downloaded. This is an option in the MEETING COMMUNICATOR in the video and PDF downloader. You can require that the recipient must login to download the documet and you can maintain an audit trail of who downloaded what and when.
Prevention is Better than a Cure
The addage holds good. It is easier to be prepared for what is likely than it is to fix the consequences. Understanding frequently encountered phishing and other scams, malicious e-mail spam, accessing public wi-fi and paying attention to the spelling of service providers names is important. Malicious attacks are often mounted from similarily named vendors to those that you may use.
Level One Strategy
Your assessment of likelyhood and impact will dictate but where information is sensitive you should, as a minimum:
Conclusion
We offer the above for your consideration but cannot suggest that the suggestions are complete nor that they will be effective in the face of a threat that you may face.
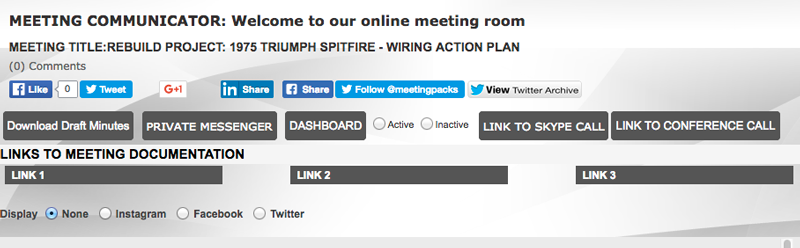
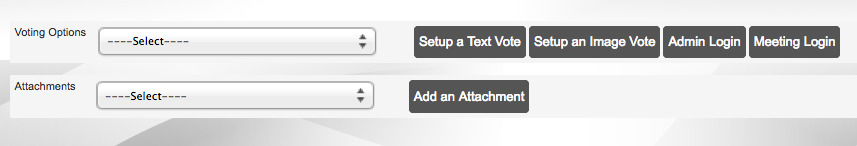
Meeting Introduction The "All Options" MeetingNote: This is a mockup meeting with all options activated The social media integration that is evidenced above by the like, share, follow & archive buttons are presented for illustrative purposes. Some meetings will be public meetings. The Fashion Group (our mockup company) may wish to host an online Q&A on Fashion Trends. This event could host a free conference call for up to 1,000 people and it would be promoted on the social media. For a normal board meeting, set behind password and login requirements, social media options would not be selected. All buttons and links on this page can be activated or deactivated. Page window sliders. There are 6 page window sliders on this webpage. The first two are presentation pages set up by the meetings site administrator. These would typically be loaded before the meeting. All six have vertical sliders. The one below this one has both a vertical and a horizontal slider to accommodate large maps, building plans etc. Click the read more option and the window will pop up to a larger page with sliders. The window styled page design is so that you can position the content in any window so as to reference it to other page windows. This page may be a presentation the fourth could be the agenda, the fith the decisions and the sixth the action plan. Any window not loaded with content will not show. Content Communication This Scroll Box Window is the first of two. The second is below. They both have fixed window sizes to enable them to both be visible on the Meeting Room Wall throughout the meeting. This one has a vertical slider that allows you to scroll the text to a paragraph that may be under discussion elsewhere. It may be used for a constitution or a legal Act. It could be used for a large table of contents so that you can position it to see where you are in the discussions on the contents listed. If no content is loaded then this window will not show. The next Scroll Box Window is designed to accommodate large images. It too has a fixed size window but allows for the content that is visible to be moved with a vertical and a horizontal slider. It is useful for building plans, project progress charts, engineering designs, development plans or as seen below screen shots. We have listed below screen shots of the actual build pages used for this meeting. It not loaded with content the page below too will not show on the Meeting Wall. An Overview of the Meetings Communicator Admin Panel Options
3. Add Links to Meeting Room Wall
4. Other setup options
5. Add Partner Links These are image links that can be placed at the foot of the site pages. The Meeting Administrator
Meeting Attendees
Meeting Introduction OUR OVERVIEW VIDEO TRANSCRIPT& QUICK START GUIDEThis post offers the transcript of the "About Us" overview video that is loaded to the site from the YouTube feed. It is open for comment on matters of clarification and I would welcome any suggestions or comments that you may have.
Hello, I am Alan Mackenzie the founder of Webo.
The Meetings Communicator is a Specialist Product of ours dedicated to addressing the need for online meeting packs and for online meeting support. Should either of these be needed we are the solution that you are looking for.
One of our unique features is that we have as a foundation a comprehensive WYSIWYG website builder.
The Meetings Pack Communicator is an online bookmarklet APP.
The Meeting Pack APP is an Alerts, Link and List Communicator
Using the Meeting Pack Communicator you are assured that the content is complete and up-to-date, well presented and conveniently available on hansets and PC's.
Once setup a virtual meeting room ensures that your meetings will be economic, effective and efficient.
On the record deliberations are typed by a meeting administrator who maintains a backoffice in support of a "Meeting Wall."
The meeting wall will allow for
In support of this we offer off the record one on one private text messsaging and one to all chat
Why us
There are ten steps to hosting your first meeting. These are:
Thank you for your time. You will find a transcript of this video on the BLOG at www.meetingscommunicator.com where you will find links to all the pages, the meeting pack and the meeting wall referenced in this video. I look forward to your questions on the blog.
Thank you
Some Bonus Detail:
The ten steps.
1. Appoint a Site Administrator to mange the setup options and a Meetings Administrator to type the meeting minues in the meeting room backoffice
2. Gather Content & Build Meetings Pack APPs by linking to original format pages or to specialist Webpages
3. Setup Meetings Categories
4. Add Meetings & Design the Meeting Wall's Structure by selecting from the range of options
5. Add to the Minute Pages Template Library by adding company specific meeting minute templates
6. Add Meeting Presentation Content to Specialist Webpages and link these to the Meeting Wall Minute pages
7. Distribute Meeting Packs with a link to the meeting wall Our Meeting Pack APP is unique. You can detail alerts on the home screen and link to tap to dial lists of telephone numbers, e-mail addresses, urls or to thousands of content pages hosted on specialist webpages.
8. Appoint and provide login details to the Meetings Administrators to take the Meeting Minutes
9. Host the Meeting Our meeting wall is also unique as it allows you to have scroll box windows open on up to six meeting minute pages at once with on and off record chat, optional social media integration, draft minute downloads, presentation sharing and opinion polling.
10. Manage Comments, Comment Followers, Voting Detail and Draft Minute finalisation
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||